How to Self-Host Behind CGNAT — Bypass Carrier-Grade NAT
CGNAT in one paragraph. Carrier-grade NAT (CGNAT) is when your ISP shares a single public IPv4 address across hundreds of customers instead of giving you your own. Outbound browsing still works, but nobody on the internet can connect in to a server running at your address — so self-hosting, game servers, email, and remote access are all broken. The fix is to get a real public IP that isn't behind your ISP's shared pool.
Skip the reading — need a real public IP in 5 minutes? Get a dedicated static IPv4 + IPv6 delivered to your existing server over an encrypted tunnel. No router changes, no ISP negotiations, works behind the strictest CGNAT.
If your internet service provider (ISP) sits you behind carrier-grade NAT (CGNAT), you can't host anything at home. Game servers don't accept connections. Self-hosted email goes nowhere. Home Assistant is unreachable from outside the house. This guide explains what CGNAT is, how to check if you're stuck behind it, which ISPs use it, and most importantly, how to get a real public IP address so you can actually host what you want to host.
What is CGNAT? (Plain English)
Carrier-grade NAT (CGNAT) also called CGN or large-scale NAT (LSN) is a way for your ISP to share a single public IPv4 address among hundreds or thousands of customers. Your home router already performs NAT (translating your devices' private addresses to the public address assigned to your line). CGNAT adds a second translation on top: your ISP takes what looks like a public IP on your router and translates it again to their shared public IP before it reaches the internet.
The result for you is that you don't actually have a public IP of your own. You have a share of one. CGNAT is invisible for everyday browsing, streaming, or video calls, your outbound connections still work; but it breaks any service that relies on other people reaching you: self-hosted websites, email, VoIP, game servers, Minecraft servers, remote desktop, Home Assistant remote access, and so on.
Why ISPs use CGNAT
The IPv4 address space, about 4.3 billion unique addresses total, was fully allocated years ago. Rather than push every customer to IPv6 (which many services and apps still handle poorly), ISPs increasingly reuse a small pool of public IPv4 addresses across customers using CGNAT. It's cheap, invisible to most subscribers, and lets them keep adding new customers without buying IPv4 blocks on the secondary market where prices have climbed to $40+ per address. RFC 6598 reserved the 100.64.0.0/10 address range specifically for this purpose.
How does Network Address Translation (NAT) work?
Network Address Translation (NAT) is a fundamental networking technique that enables multiple devices on a private network to share a single public IP address when accessing the internet. NAT acts as an intermediary between your local network and the broader internet, translating private IP addresses (like 192.168.1.100) into public IP addresses that can be routed across the internet. It has become essential in modern networking because of the limited availability of IPv4 addresses and the need for network security. By implementing NAT, organizations and home users can conserve public IP addresses while maintaining connectivity for many devices simultaneously.
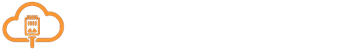
The primary function of NAT is maintaining a translation table that maps internal private IP addresses and port numbers to external public IP addresses and ports. When a device on your private network initiates an outbound connection, the NAT device (typically a router or firewall) replaces the source IP address and port with its own public IP address and an available port number. This process ensures that return traffic can be properly routed back to the originating device. NAT operates at the network layer (Layer 3) of the OSI model and is transparent to end users, meaning devices on the internal network can communicate with external resources without requiring individual public IP addresses.
What happens when device A connects to a website
- Device A sends a packet (
192.168.1.100:12345→203.0.113.10:80) - The router translates the packet to (
202.88.69.1:7771→203.0.113.10:80) and records an entry in its NAT table - The web server receives a packet from
202.88.69.1:7771
The reply flow from website to device A
- Website responds (
203.0.113.10:80→202.88.69.1:7771) - The router uses the NAT table to translate the packet (
203.0.113.10:80→192.168.1.100:12345) - Device A receives the response
How does carrier-grade NAT (CGNAT) work?
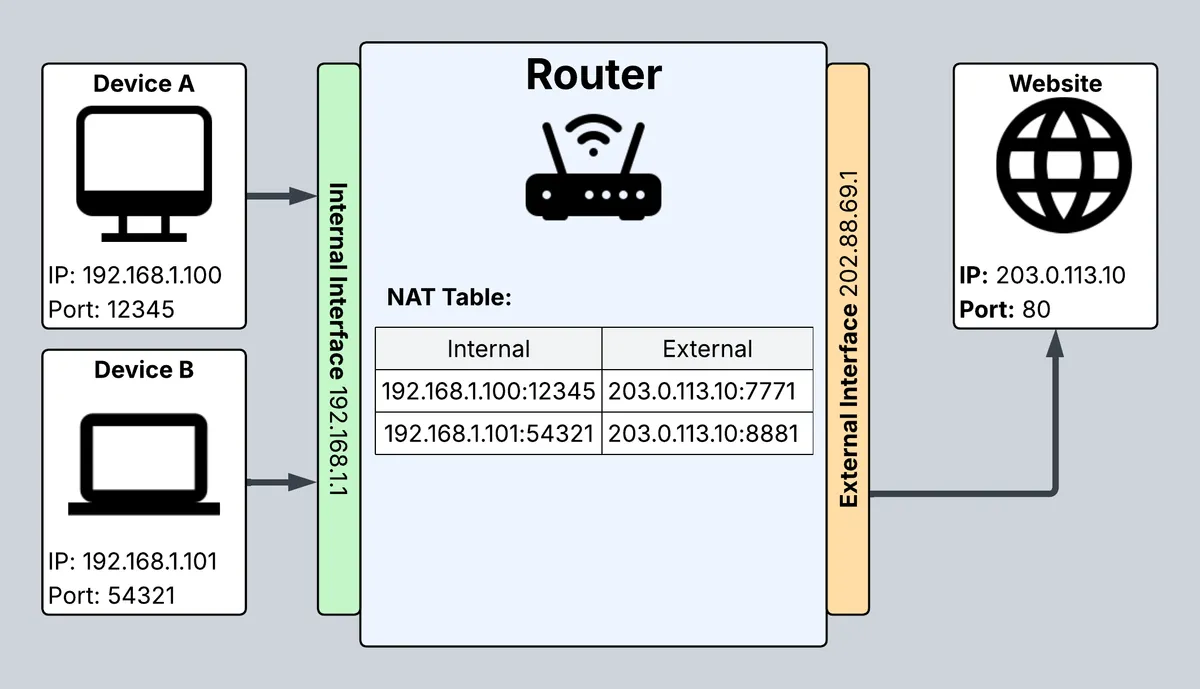
Carrier-grade NAT works the same way as your home or office NAT, the end result is simply two layers of NAT between your devices and the internet. It lets multiple ISP subscribers share a single public IP address, which saves the number of public IP addresses needed for all users on the internet and allows the internet to keep growing on a limited pool of IPv4 addresses.
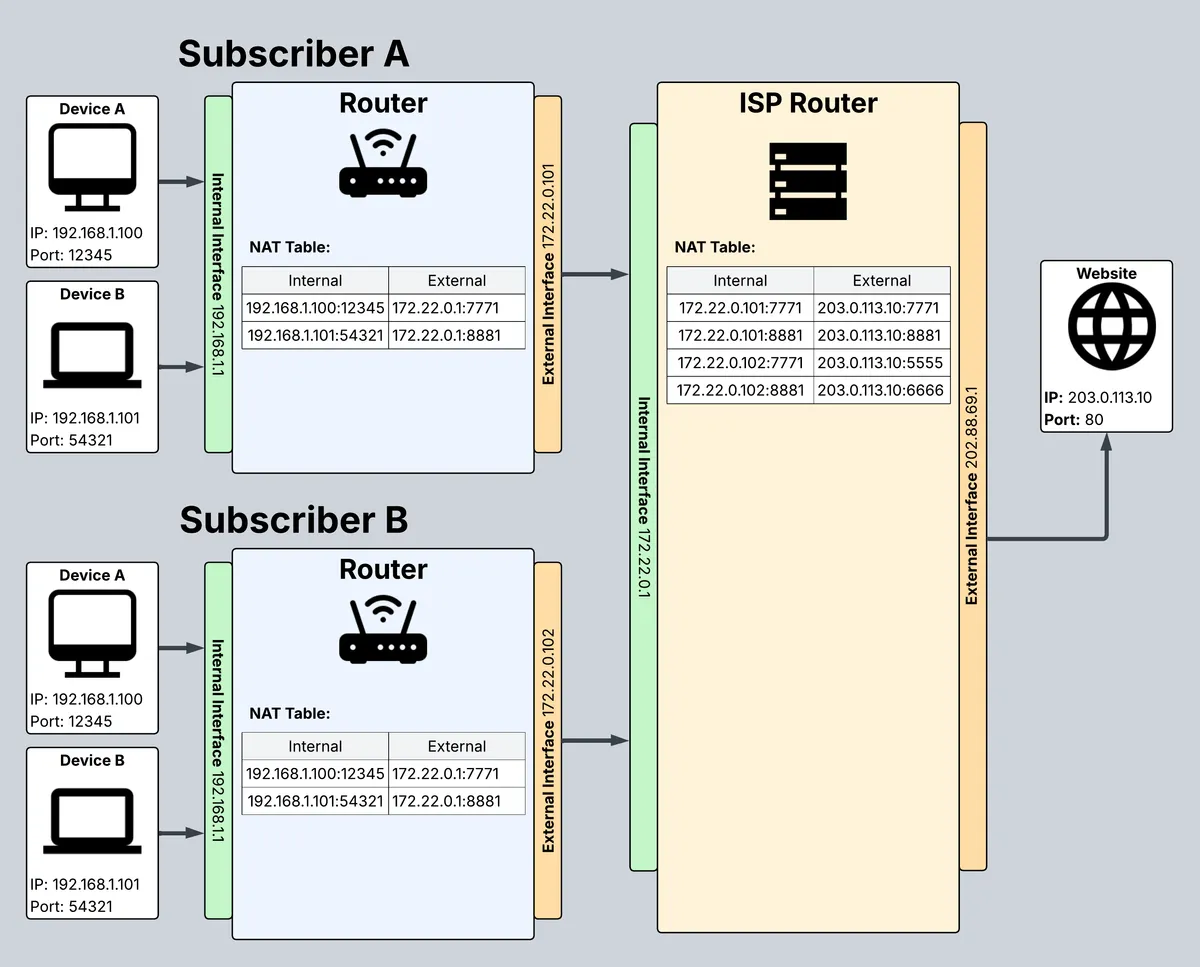
What happens when subscriber B's device B connects to a website
- Device B sends a packet (
192.168.1.101:54321→203.0.113.10:80) - The home / office router translates the packet (
172.22.0.102:8881→172.22.0.1:8881) and maintains its own NAT table - The ISP then translates the packet again (
202.88.69.1:6666→203.0.113.10:80) and maintains a separate NAT table - The web server receives the packet from
202.88.69.1:6666
The reply flow from the website
- Website responds (
203.0.113.10:80→202.88.69.1:6666) - The ISP router uses the NAT table to translate the packet (
203.0.113.10:80→172.22.0.102:8881) - Your home / office router uses its NAT table to translate the packet (
172.22.0.1:8881→192.168.1.101:54321) - Subscriber B's device B receives the response
The CGNAT IP address range (100.64.0.0/10)
CGNAT uses a reserved IPv4 range defined in RFC 6598: 100.64.0.0 to 100.127.255.255, written in CIDR notation as 100.64.0.0/10. That's roughly 4 million addresses, enough for an ISP to stand up a large customer base without conflicting with any public internet address or the private RFC 1918 ranges (10.x.x.x, 172.16–31.x.x, 192.168.x.x) that home routers use.
The practical signal: if your router's WAN interface shows an address starting with 100.64. through 100.127., your ISP is using CGNAT. You can check this in your router's admin panel (usually under "WAN" or "Status → Internet") or from a computer on the LAN by visiting the router's admin page.
Not every CGNAT deployment uses this range, some ISPs deploy CGNAT on other unallocated blocks, but 100.64.0.0/10 is the standard and the most common signal.
How to check if you're behind CGNAT
Three quick tests. Any one of them confirms CGNAT.
1. Compare your router's WAN IP to your real public IP
Log into your router's admin panel and note the WAN / public IP it reports. Then, from any device on your network, run one of these commands to see what the internet actually sees you as:
curl https://api.getpublicip.com/ip
# or
wget -O- https://api.getpublicip.com/ip
If the two IPs don't match, you're behind CGNAT (or some other kind of upstream translation). See our full guide to finding your public IP on Linux for more commands and alternatives.
2. Check for a 100.64.x.x address on your router's WAN
If your router's WAN interface shows an address in the range 100.64.0.0 - 100.127.255.255, that's the reserved CGNAT range, your ISP is definitely using CGNAT.
3. Try to open a port from the outside
Pick an unused port (say, 8080), forward it on your router to a test service, and try to connect from a phone on mobile data or from a friend's network. If the connection times out and everything in your setup looks correct, CGNAT at the ISP level is the likely cause. You can also call your ISP and ask directly: Am I on CGNAT? Can I get a public IPv4 address on my plan?
Which ISPs use CGNAT?
CGNAT is most common on mobile networks (4G / 5G) and increasingly on fibre broadband in markets where IPv4 is scarce. The list below is not exhaustive, and individual plans or customer cohorts within an ISP may differ, use the three checks above to confirm your own situation.
| ISP | Country | Status | Notes |
|---|---|---|---|
| Virgin Media | UK / Ireland | Partial | Rolled out to new subscribers in Ireland; UK residential mostly still public |
| Tele2 | Sweden / Baltics | Confirmed | Mobile and residential fibre |
| Simba (formerly TPG Telecom SG) | Singapore | Confirmed | Shared IPv4 across customers on residential fibre |
| StarHub | Singapore | Partial | Some residential broadband plans |
| Singtel | Singapore | Partial | Mixed - depends on plan tier |
| 2degrees | New Zealand | Confirmed | Mobile and some residential |
| TPG / iiNet | Australia | Partial | Some NBN plans |
| Hyperoptic | UK | Confirmed | Residential fibre by default |
| Community Fibre | UK | Confirmed | Residential fibre by default |
| Cox Communications | US | Partial | Cox Mobile; residential broadband generally public |
| FPT Telecom | Vietnam | Confirmed | Residential fibre |
| Viettel | Vietnam | Confirmed | Residential fibre |
| VNPT | Vietnam | Confirmed | Residential fibre |
| Most mobile / 4G / 5G networks | Worldwide | Confirmed | CGNAT is effectively the default on mobile data |
If your ISP isn't listed, don't assume you're in the clear. Some ISPs offer a static IP add-on as a paid upgrade that takes you out of the CGNAT pool, if that's not an option, read on.
CGNAT vs static IP vs Cloudflare Tunnel vs GetPublicIP
Four realistic ways to get inbound connectivity at home despite CGNAT. Each has trade-offs.
| Solution | Inbound connections | Email hosting | SSL/TLS terminates | Typical cost | Portability | Failover |
|---|---|---|---|---|---|---|
| ISP static IP | Yes | ⚠️ Poor reputation | At your server | $5–$30 / month (often business-only) | ❌ Tied to your line | ❌ None |
| Cloudflare Tunnel | HTTP(S) only | ❌ Not supported | At Cloudflare | Free on Zero Trust free tier | ✅ Yes | Via Cloudflare |
| Tailscale / mesh VPN | Only for invited peers | ❌ No public email | End-to-end | Free tier / $6+ per user | ✅ Yes | Depends on setup |
| GetPublicIP | Any protocol | ✅ Full SMTP/IMAP | At your server (end-to-end) | Flat monthly per IP | ✅ Move your server anywhere | ✅ Built-in |
ISP static IP
Ask your ISP. Some offer it for an extra monthly fee, usually on business plans only. You get a real, dedicated public IPv4. Downsides: residential-IP blocks often have poor mail sender reputation (which breaks email hosting), you lose the IP if you move house, and there's no failover if your line goes down. Our full walkthrough: how to get a static IP address.
Cloudflare Tunnel
Free and works, for HTTP(S) only. Cloudflare reverse-proxies your traffic through their edge, so SSL/TLS is terminated on Cloudflare's servers. That's a dealbreaker if you need true end-to-end encryption or you're hosting anything beyond web services (email, game servers, VoIP, SSH over a custom port, etc.). See our detailed comparison: GetPublicIP vs Cloudflare Tunnel vs Tailscale.
Tailscale / mesh VPN
Great if the only people connecting to your server are you and a small circle you can invite onto the VPN. Not suitable for anything that needs to be reachable on the open internet, your services aren't visible to non-members.
GetPublicIP
A dedicated public IPv4 hosted on our edge infrastructure, routed to your server via a WireGuard tunnel. Your server initiates an outbound connection to us (which CGNAT allows), and all inbound traffic for your public IP flows back through that tunnel. SSL/TLS is end-to-end encrypted, we never see your plaintext. Works for any protocol. Portable across locations. Built-in failover.
How does GetPublicIP work?
GetPublicIP delivers a public IP address over an encrypted WireGuard VPN tunnel to your server in your home or office. This solution overcomes carrier-grade NAT and lets you relocate your server to another location without needing to change your IP address, unlike ISP static IP addresses, which are tied to the physical line.
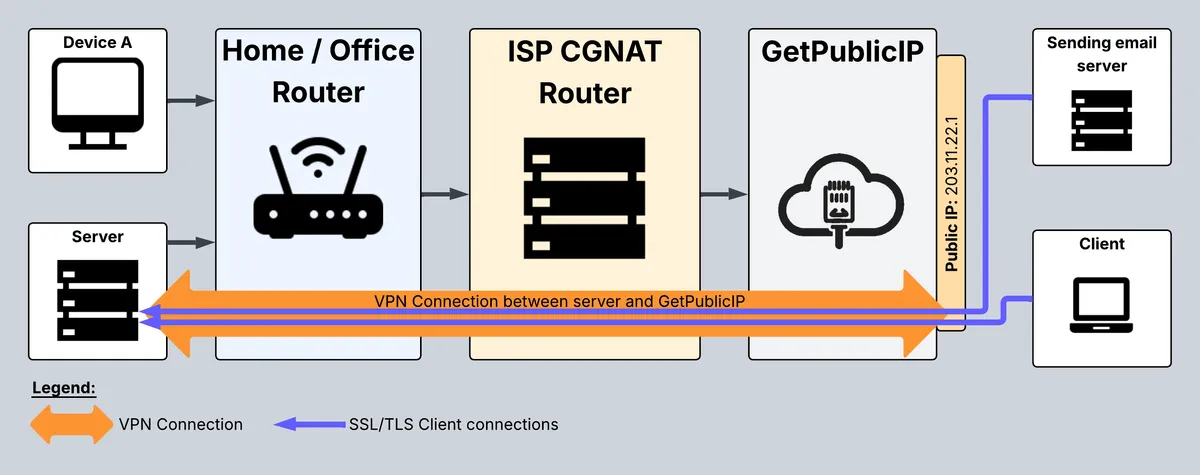
How it works
- Your server connects to the GetPublicIP server. This outbound connection sets the NAT tables between your server and GetPublicIP's server and creates a path for communication something CGNAT allows without issue.
- When remote clients connect to your public IP address, the packets are sent through the encrypted VPN tunnel to your server.
- The SSL / TLS connection between the client and your server is end-to-end encrypted with your own SSL certificates. It starts at the client and ends at your server, we never see the plaintext.
Ready to try it? Create an account or start with the getting-started guide.
Frequently Asked Questions
What is CGNAT (carrier-grade NAT)?
Carrier-grade NAT (CGNAT), also known as large-scale NAT (LSN) or CGN, is a technique internet service providers use to share a single public IPv4 address among hundreds or thousands of customers. Your ISP translates your traffic at their network edge, meaning you no longer have a dedicated public IP. It conserves scarce IPv4 addresses but breaks inbound connections, so you cannot host servers, run game hosts, or reliably use services that need a reachable address.
Why do ISPs use CGNAT?
IPv4 addresses ran out. There are only about 4.3 billion IPv4 addresses in existence and they have all been allocated. Rather than force every customer onto IPv6 (which many services still do not support), ISPs share a single public IP across many subscribers using CGNAT. It is cheap, invisible to most users, and lets them keep adding customers without buying expensive IP blocks on the secondary market.
How do I know if I am behind CGNAT?
Check your router's WAN IP address and compare it to your actual public IP (run curl https://api.getpublicip.com/ip from a device on your LAN, or visit any what-is-my-IP site). If the two do not match, or if your router shows an address in the 100.64.0.0/10 range (100.64.x.x through 100.127.x.x), you are behind CGNAT. You can also try opening a port in your router, if external connections never arrive, CGNAT is almost certainly the cause.
What is the CGNAT IP address range?
The reserved range for CGNAT is 100.64.0.0/10, defined in RFC 6598. This gives ISPs about 4 million addresses (100.64.0.0 through 100.127.255.255) to use internally for CGNAT without colliding with any public internet address or private RFC 1918 range. If you see one of these addresses on your router's WAN interface, your ISP is using CGNAT.
Can I self-host servers behind CGNAT?
Not directly. CGNAT breaks inbound connections because your ISP's NAT does not know which customer to forward an incoming packet to. You need one of four workarounds: request a static IP from your ISP, use Cloudflare Tunnel (works but terminates SSL on Cloudflare's servers), use Tailscale or a similar mesh VPN (works only for people you invite), or use a dedicated public-IP service like GetPublicIP that routes a real static public IP to your server over an encrypted tunnel.
Which ISPs use CGNAT?
Many worldwide, especially in mobile and fibre markets where IPv4 is scarce. Commonly reported CGNAT ISPs include Virgin Media (Ireland), Tele2 (Sweden and Baltics), Simba and StarHub (Singapore), 2degrees (New Zealand), TPG and iiNet (Australia), Hyperoptic and Community Fibre (UK), Cox Mobile (US), and Vietnam's FPT, Viettel, and VNPT. Most mobile and 4G/5G networks globally use CGNAT by default. Some ISPs offer a public-IP opt-out for a fee.
Is CGNAT the same as double NAT?
They are related but not identical. Any home router performs NAT (private LAN to public IP). CGNAT adds a second NAT layer at the ISP (their private range to a shared public IP), creating a double-NAT scenario. The symptoms are similar, broken inbound connections, port forwarding does not work, UPnP is unreliable, but CGNAT is caused by your ISP, not your own equipment, so changing your router will not fix it.
What is the difference between CGNAT and a public IP?
A true public IP is unique to you on the internet and is reachable from anywhere by default (subject to your own firewall). A CGNAT address is shared with many other customers and is not reachable from the outside, you can browse the web and initiate connections, but nobody can connect in to a server running at your address. If you need inbound connectivity (servers, email, games hosted at home, remote desktop), CGNAT is a dealbreaker.
Does a static IP from my ISP solve CGNAT?
Yes, if your ISP actually offers it. A static IP from your ISP takes you out of the CGNAT pool and gives you a dedicated public address. The downsides: it is usually expensive (especially on residential plans), tied to your physical line (moving house means losing it), often has poor email-sender reputation, and many ISPs do not offer static IPs to residential customers at all.
How does GetPublicIP bypass CGNAT?
GetPublicIP gives you a dedicated public IPv4 address hosted on our edge infrastructure, then tunnels traffic to your server via WireGuard. Your server makes an outbound connection to us (which CGNAT allows fine), and we forward all inbound traffic for your public IP through that tunnel. SSL/TLS is end-to-end encrypted, we never see your plaintext. The result is a real static public IP, portable across locations, no router changes, works even behind the strictest CGNAT.